 You may find you install a SSL cert, but certain browsers show the connection as unsafe (i.e. mobile browser has issues but desktop browsers are happy)
You may find you install a SSL cert, but certain browsers show the connection as unsafe (i.e. mobile browser has issues but desktop browsers are happy)
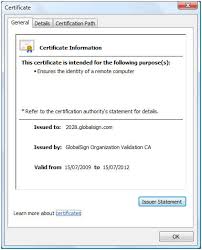
This generally points to not having the cert chain correct. You can check your cert chain at sites like –
https://ssltools.websecurity.symantec.com/checker/views/certCheck.jsp
https://www.sslshopper.com/ssl-checker.html
- Download your Intermediate and Primary Certificates.
- Open a text editor (such as notepad) and paste the entire body of each certificate into one text file in the following order:
- The Private Key – your_domain_name.key
- The Primary Certificate – your_domain_name.crt
- The Intermediate Certificate – gd_bundle_g2_g1.crt
- The Root Certificate – TrustedRoot.crt
Make sure to include the beginning and end tags on each certificate. The result should look like this:
—–BEGIN RSA PRIVATE KEY—–
(Your Private Key: your_domain_name.key)
—–END RSA PRIVATE KEY—–
—–BEGIN CERTIFICATE—–
(Your Primary SSL certificate: your_domain_name.crt)
—–END CERTIFICATE—–
—–BEGIN CERTIFICATE—–
(Your Intermediate certificate: DigiCertCA.crt)
—–END CERTIFICATE—–
—–BEGIN CERTIFICATE—–
(Your Root certificate: TrustedRoot.crt)
—–END CERTIFICATE—–Save the combined file as your_domain_name.pem. The .pem file is now ready to use.