Cloudflare are nice enough to provide a free tier to their CDN service which is perfect for those of us that still host websites at home. The free teir provides some basic benefits – DDOS protection and caching. Check out the details here – https://www.cloudflare.com/plans/#overview
If you utilize their tunneling solution, you’ll also be able to host websites behind a dynamic IP. You’ll no longer need a static IP. This means the traffic goes like so;
Your website <-> ACME <-> Cloudflare tunnel <-> Cloudflare <-> User
Double cool! Check out these resources to do it for yourself –
ACME Manager : https://hub.docker.com/r/jlesage/nginx-proxy-manager/
Cloudflared (Tunnel) container : https://hub.docker.com/r/cloudflare/cloudflared/
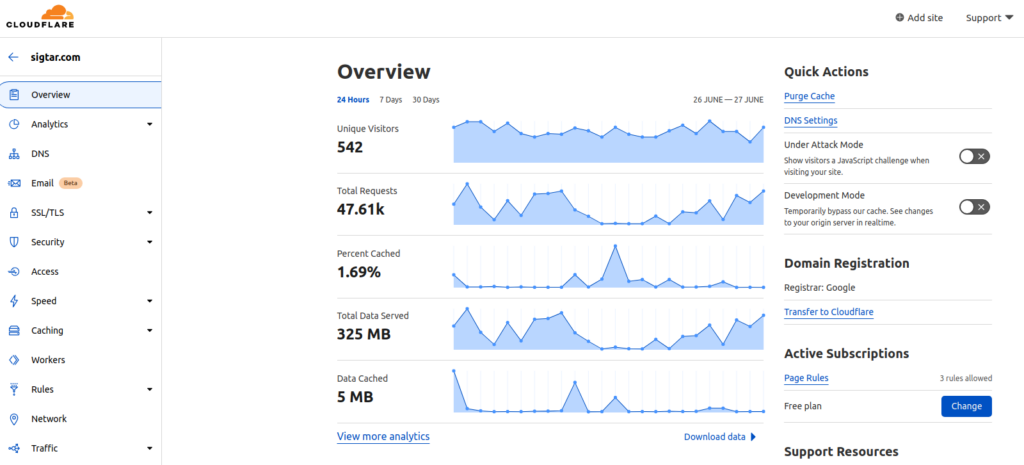
Example results over 24hrs for sigtar.com –
 Brave is a web browser that has been about for while, but i only happened across it when it made its way onto the android platform.
Brave is a web browser that has been about for while, but i only happened across it when it made its way onto the android platform.